API Runtime Protection
Runtime Content validation, threat detection and traffic throttling
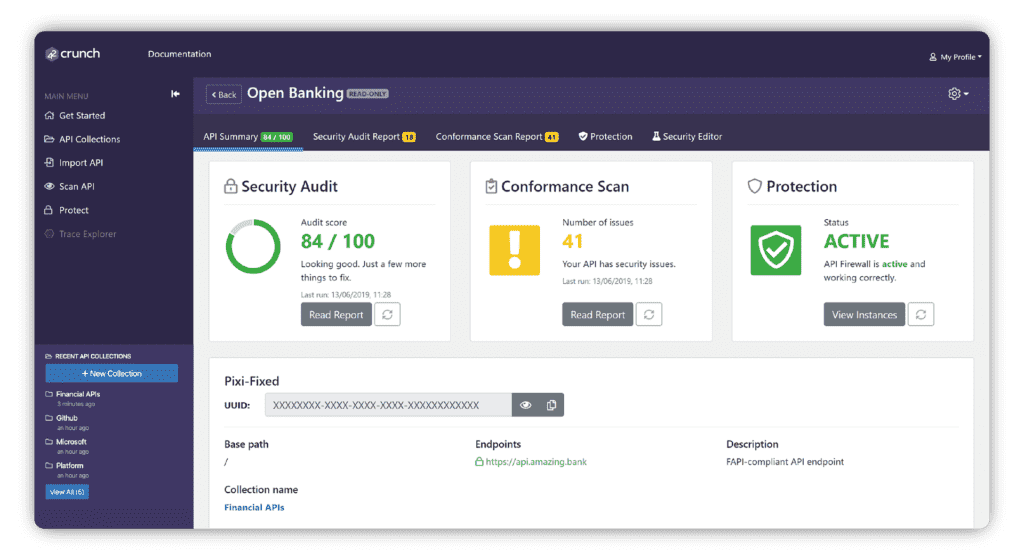
API Protection is a critical capability of an API security platform. It relates to the ability to enforce security policies at design and runtime typically using an API micro-firewall.
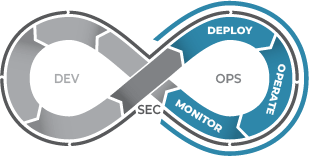
Shift-Left and Shield-Right for API Protection
Unlike traditional Appsec testing or firewall tools (SAST, DAST & WAF) or newer API behavior analysis tools, 42Crunch combines a shift-left (API security testing during design, development and testing) and a shield-right (runtime protection) approach to API security. From design-time right through to run-time, 42Crunch protects your APIs throughout the API lifecycle against API threats.
Automatically Enforce Content validation
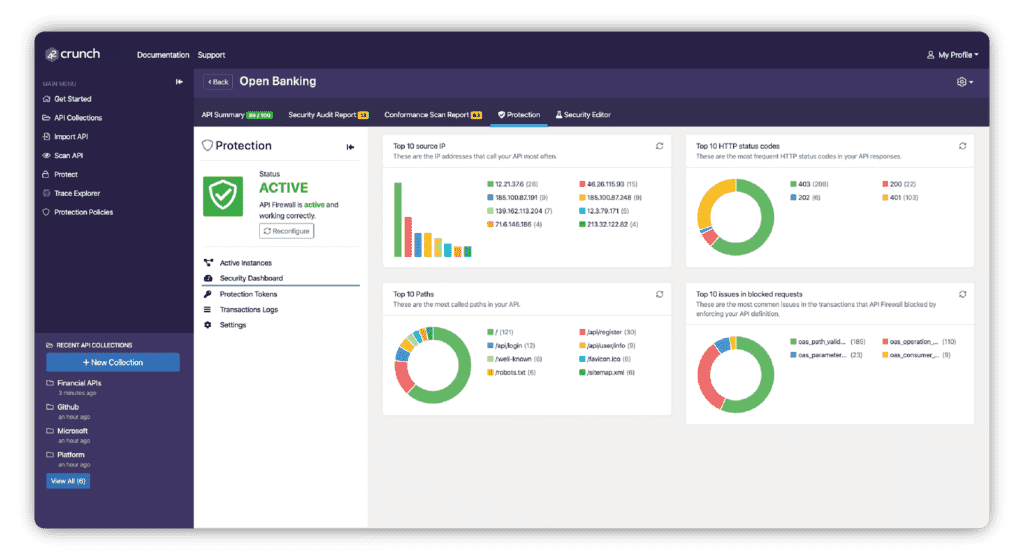
Deploy API Protection directly from your CI/CD pipeline and it reconfigures automatically whenever the OpenAPI contract changes. API Protection is tailored to protect each API using a positive security model based on data conformance to the OpenAPI contract, block malicious attacks and unlike a traditional WAF-based solution, distinguish API attacks from legitimate API content traffic.
Threat Prevention and Anomaly Detection
WIth 42Crunch you can detect OWASP API Security Top 10 issues such as data leakage, overflows, mass assignment, broken authentication or security misconfigurations. Our platform detects vulnerabilities triggered by the usage of:
- Wrong verbs (invoking the API with GET or HEAD) when it expects PUT
- Wrong paths
- Wrong content-type
- Wrong data format (integer instead of string for example)
- Outside of API constraints (large strings, numbers or arrays)
- Data Injection

Traffic Throttling
By throttling traffic based on a range of criteria, 42Crunch actively enforces API protection to prevent Denial of Service (DoS) or brute-force attacks. In microservice deployments, API Protection is deployed separately with each instance of the microservice, so rate limiting is also enforced separately on each instance.
Secure Your APIs Today
#1 API security platform