Security Ready API Security by Design
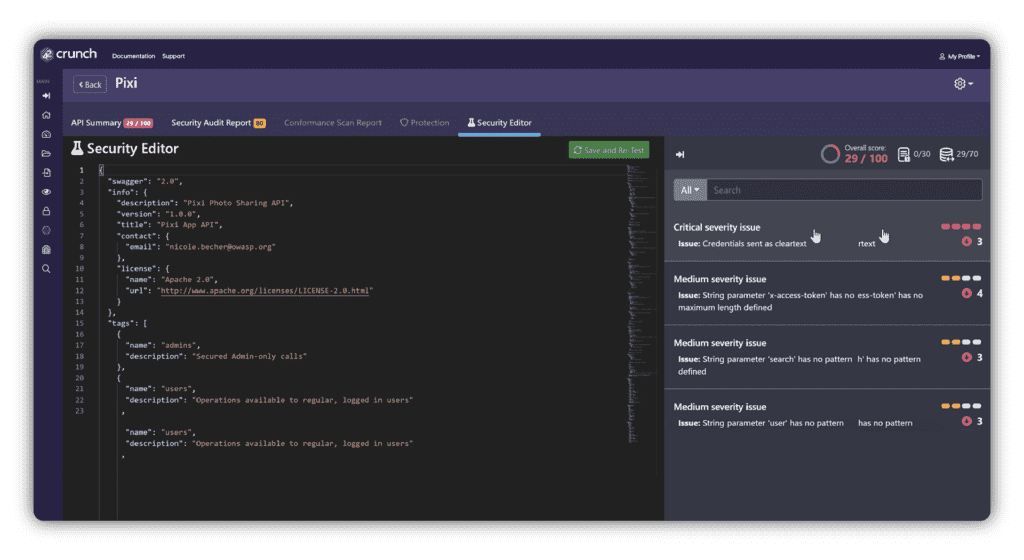
42Crunch ensures that all your APIs meet the requisite security standards before deployment. Run a security audit on the OpenAPI contract, scan the live API endpoints for potential vulnerabilities, and automate the redeployment of runtime protection policies with each API change making sure that you can stay agile and enforce a zero-trust architecture.
Security
Turn error-prone manual API security into a fool-proof production deployment.
Turn error-prone manual API security into fool-proof deployment
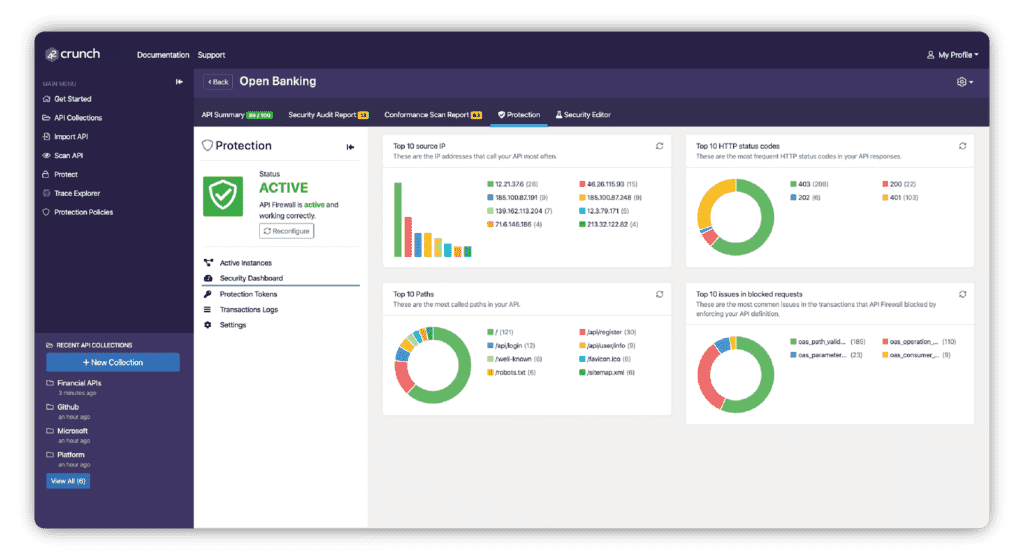
API audit and API scanning are automated checks ensuring that unsecure APIs never make it to the master branch and production deployment. Runtime protection policies are automatically redeployed with each API change making sure you stay agile without compromising security. Thanks to its low footprint, API Protect can be deployed at scale on any container orchestrator such as Kubernetes, Amazon ECS or Red Hat OpenShift(®).
Our runtime is fully compatible with existing API management solutions or API gateways and with microservices-based architectures. We support the sidecar proxy and gateway deployment models.
Consistent enforcement of threat protection policies across platforms and frameworks
With our API security platform, enterprises can centrally enforce and monitor corporate security policies, using API tools that have been designed both to be API-centric and to work together. Security teams get full visibility of the entire API portfolio, including audit grades, usage, blocked attacks, and potential vulnerabilities.
Rules-free automatic threat protection
The API contract becomes the core of the positive security model of our API Firewall, and policies are tailored automatically to each and every API. This virtually eliminates false positives and false negatives and does not require training any AI for weeks on end to learn the model.
The API Conformance Scan completes the loop by automating tests based on the OpenAPI contract, allowing you to refine both the OpenAPI contract itself and the policies attached to the API.

360° degree view of all APIs
Benefit from a common security language and shared understanding of the APIs that the company has, their current state, security levels, production protection status, and any outstanding security improvements. 42Crunch integrates with standard SIEMs (Azure Sentinel etc.) and dedicated API runtime discovery tools (Cisco API Clarity) for vulnerability alerting.
Dr. Philippe De Ryck, Web Security Expert with Pragmatic Web Security and Colin Domoney of 42Crunch and APISecurity.io, take a deep dive into understanding and addressing the OWASP API Security Top 10 issues.

Dr. Philippe De Ryck
Secure Your APIs Today
#1 API security platform