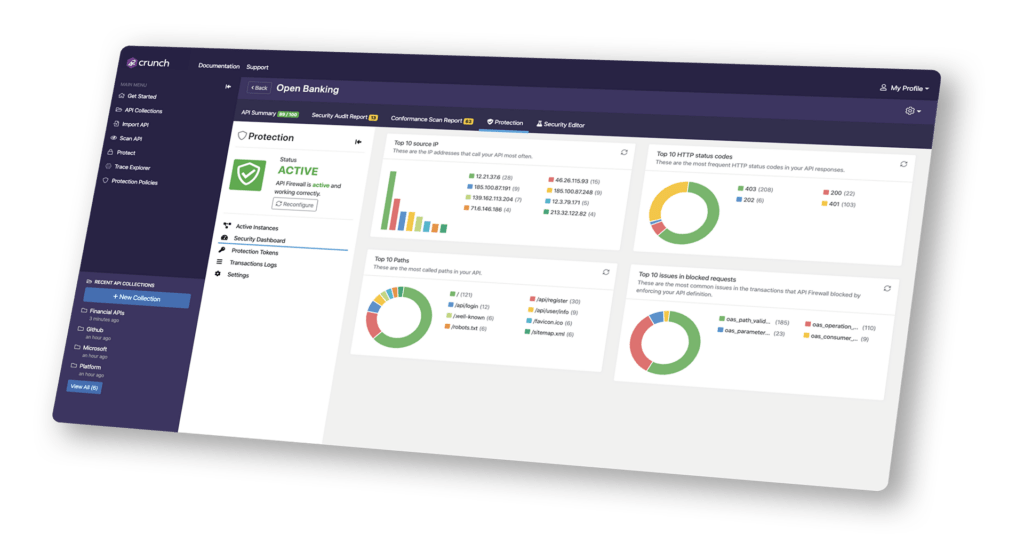
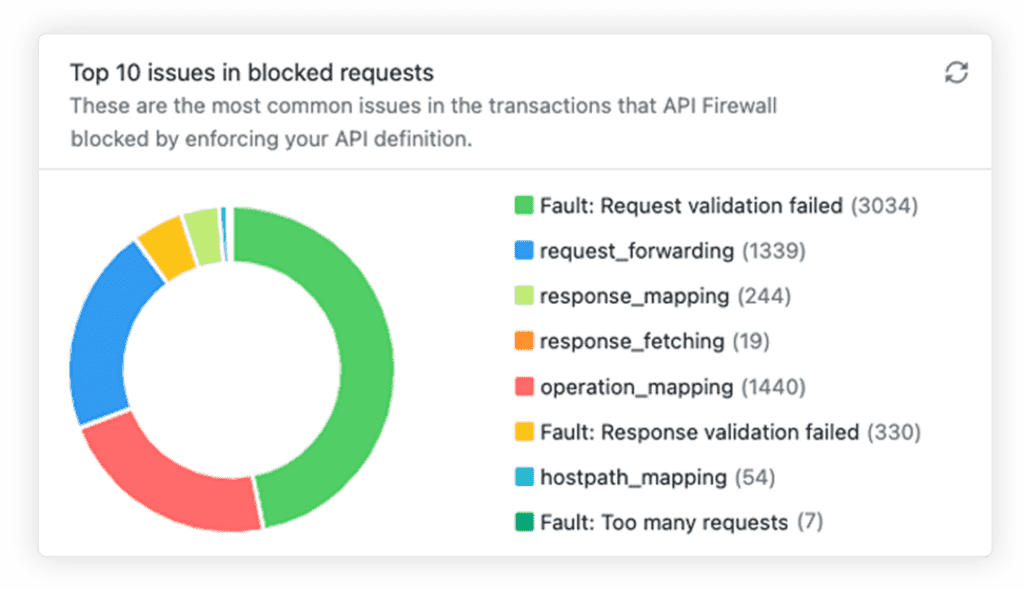
42Crunch API Protection creates an allowlist of valid operations and input data based on the OpenAPI contract. Through an API micro-firewall it enforces this configuration on all incoming as well as outgoing transactions. Transactions that do not conform to the OpenAPI definition are automatically blocked. API Protection is a core shield-right element of our API Security Platform
Automatically Apply Protection at RunTime
API Protection enforces API runtime protection directly in front of your APIs. The API Protection micro-firewall, is tailored to protect each API from malicious attacks. Unlike a traditional WAF-based solution, API Protection distinguishes API attacks from legitimate API traffic.
No manual rules, automate configuration from your CI/CD
Deploy API Protection from your CI/CD pipeline and it will automatically reconfigure each time the API changes. Our protection technology directly interprets OpenAPI definitions and constrains the API traffic on request and response.
Maximum Functionality, Minimal Latency
API Protection has been built with performance in mind and is highly optimized, it typically adds less than 1 millisecond of latency to the whole transaction, allowing you to deploy it at scale across your enterprise.
Deploy Anywhere For External & Internal API Protection
You can use our API firewall to equally protect north-south and east-west traffic. Thanks to its low footprint, it can be deployed at scale on any container orchestrator such as Kubernetes, Amazon ECS or Red Hat OpenShift(®). Our runtime is fully compatible with existing API management solutions or API gateways and with microservices-based architectures. Full support for both sidecar proxy and gateway deployment models.
Related content
Secure Your APIs Today
#1 API security platform