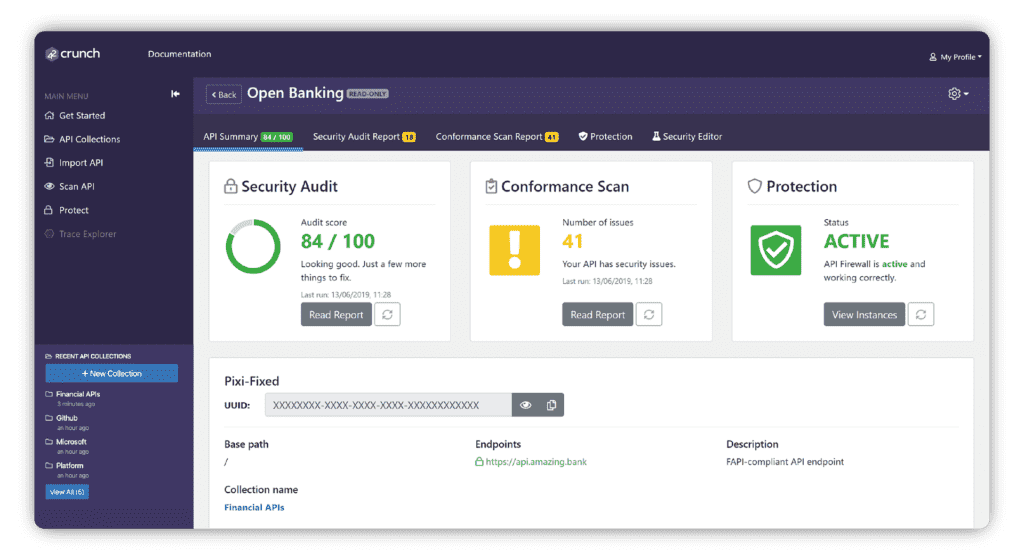
API Scan continually scans the API to ensure conformance to the OpenAPI contract and detect vulnerabilities at both testing time and runtime. It detects OWASP API Security Top 10 issues early in the API lifecycle and validates that your APIs can handle unexpected requests. The API Conformance Scan is one of the core shift-left elements of our API Security Platform.
Runtime Testing of OpenAPI Definition Compliance
API Scan provides dynamic runtime API security testing of your API to ensure your API implementation matches the contract set out in the OpenAPI definition of the API.
Bulletproof your APIs with Continuous Runtime Behavior Scanning
API Scan simulates real API traffic to test your API's behavior under load and validates if your APIs can handle or reject requests according to the OpenAPI / Swagger definition. It also flags responses which are:
- unknown (for example a HTTP 500 error occurring),
- of the wrong type (HTML instead of JSON)
- or not matching the JSON schemas described in the OpenAPI Specification.
Early Detection of OWASP API
Security Top 10 Vulnerabilities
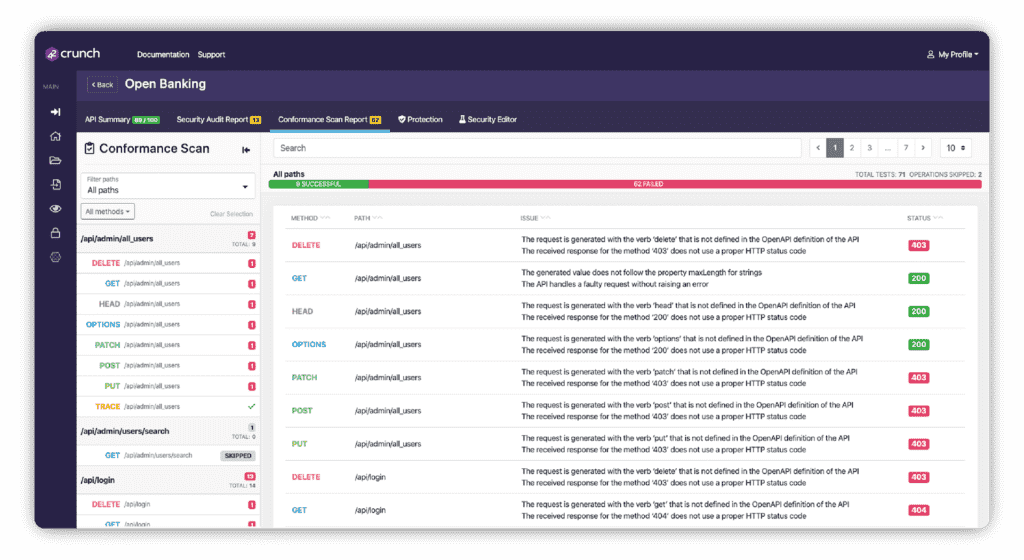
With API Scan you can detect any OWASP API Security Top 10 issues early in the API lifecycle. Identify and remediate issues such as data leakage, overflows, mass assignment, broken authentication or security misconfigurations. It detects vulnerabilities triggered by the usage of:
- Wrong verbs
- Wrong paths
- Wrong content-type
- Wrong data format
- Outside of API constraints
- Data Injection

Actionable Information
for Immediate Remediation
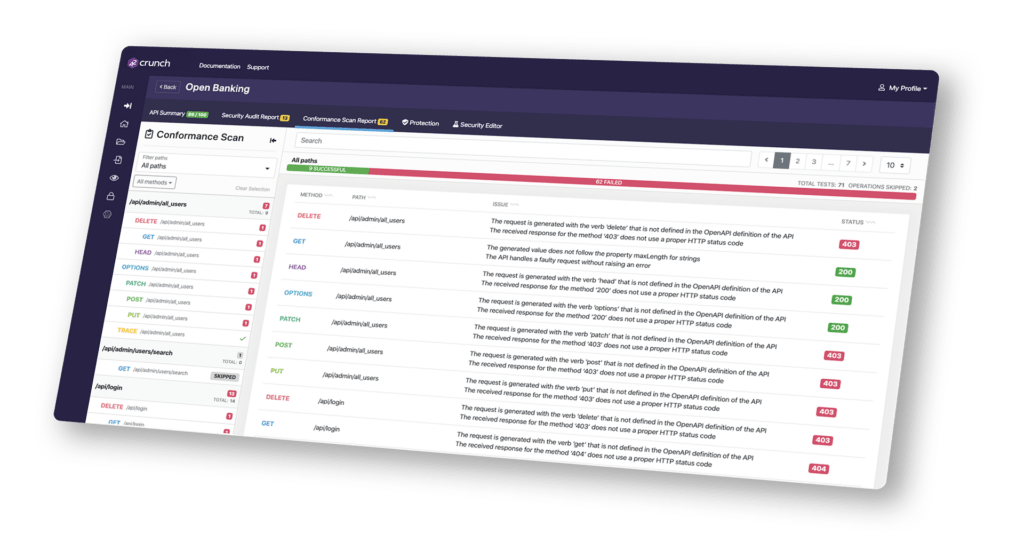
API Scan generates an immediate report that provides actionable information of how well your API conforms to its OpenAPI definition. The report summarizes all of the key issues and provides deep-dive analysis with info on the cURL requests the scan used to detect each issue.
Related content
Try API Scan for Free
- Dynamic runtime testing that simulates real traffic to your API.
- Tests conformance to the audited OpenAPI Contract.
- The instant report provides automated and guided fixes in-line with code.
Secure Your APIs Today
#1 API security platform