Webinars Upcoming and previously recorded API security-related webinars.
Gain valuable insights and advice from 42Crunch and external API security industry experts on API security best practices. Webinars cover API security topics such as common API breaches, API defense techniques, API Security Testing, OWASP API Security Top 10 vulnerabilities, 42Crunch products and tools...
New Webinars coming soon!
On Demand Webinars

Agentic AI: Fools Rush in Where Angels Fear to Tread
Join, Rik Turner, Chief Analyst at Omdia in conversation with Philippe Leothaud, CTO at 42Crunch as they separate signal from noise and explore the practical implications for enterprises seeking to enable the AI enterprise with agentic AI, but ensure that the appropriate security guardrails are in place.
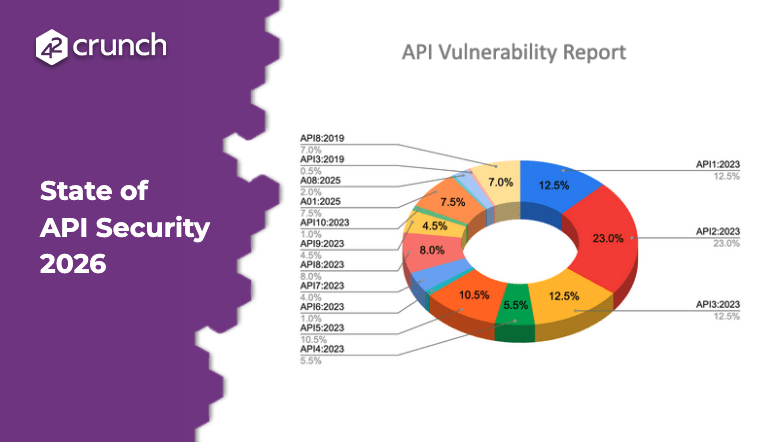
State of API Security 2026
Webinar drawing on two years of investigative research from the industry’s leading APIsecurity.io newsletter that includes cases from a wide range of independent sources, the webinar highlights the most common API flaws, from broken input validation and missing authentication to operation-level authorization failures.
OWASP BOLA, BA, BOPLA: wie man sie finded und behebt
Wir werden verstehen wie die OWASP API Top 3 von Hackern genutzt werden um Daten aus Unternehmen zu stehlen und wie man sie schon während der Implementierung findet und beheben kann.

API Security Insights for the Connected Vehicle Ecosystem
API security best practice for the automotive industry and the Vehicle Connected Ecosystem. Advice, trends and insights from Darren Shelcusky, cybersecurity consultant to the automotive industry.
Mitigate OWASP API risks through security-by-design
Learn best practices and mitigation steps for some of the OWASP API vulnerabilities through this 42Crunch API security best practice webinar

When GenAI Meets Risky APIs
42Crunch demonstrate how GenAI can be used to exploit unsecured APIs to gain unauthorized access, inject malicious prompts and manipulate data. Also learn how to prevent your APIs from being undermined by adopting a proactive API security as code approach to defending your APIs.
Review of Major API Security Breaches from H1 2024
In this latest webinar, Anthony Lonergan, reviews some of the most recent high-profile API breaches that occurred in 2024.
Anthony will give a detailed overview of each attack and explain how the different vulnerabilities could be exploited to compromise the companies involved. He then practically demonstrates how companies can remediate against these vulnerabilities order to better protect their APIs.

Navigating the depths of API security testing with 42Crunch and Microsoft
As part of the Microsoft Reactor Spotlight on GitHub Advanced Security webinar series, 42Crunch and Microsoft explore the hidden risks that threaten APIs and delve into vulnerabilities within your codebase. From scanning OpenAPI specs to dynamic testing, we equip you with practical strategies to harden your APIs against attacks.
Top Things You Need to Know About API Security
Two of the API security industry’s leading experts, Dr Philippe de Ryck and Isabelle Mauny, guide you through some real-world cases of API security attacks and also share some best practices for securing your APIs.

Something Old, Something New – OWASP API Security Top 10 in 2023
42Crunch’s Colin Domoney takes a look at the new OWASP API Security 2023 listing, identifying which vulnerabilities are new, which have not changed and which have been removed.
Mastering Secure API Development with GitHub and 42Crunch
Isabelle Mauny (Field CTO) and Colin Domoney (Chief Technology Evangelist) from 42Crunch as they take a deep dive with live demos into how 42Crunch combines with GitHub to facilitate secure API development.
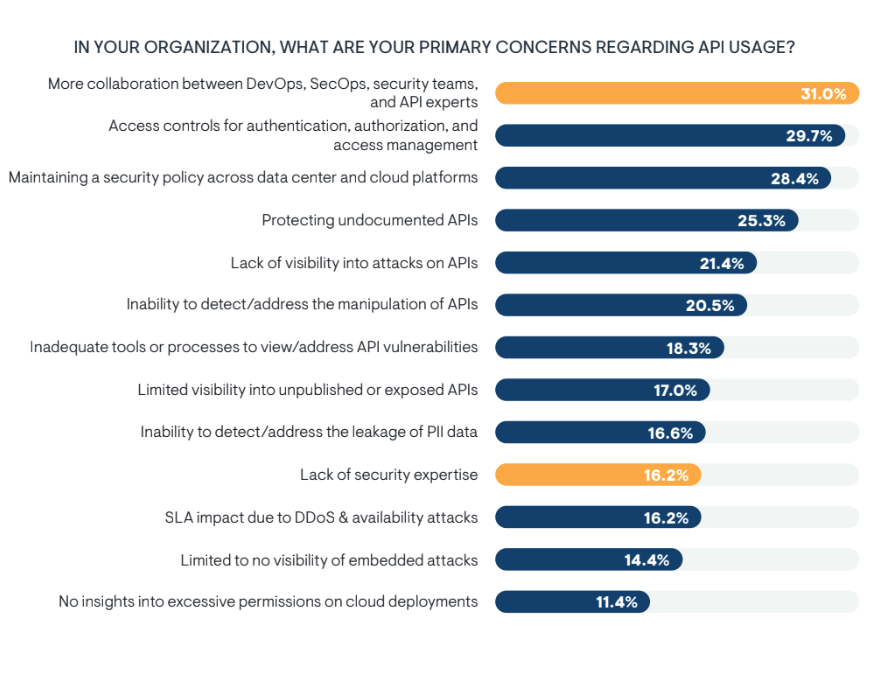
Why API Security Cannot Wait Until Production
Enterprise Management Associates’ recent survey of technology and business leaders in North America revealed that 32% of firms admitted to only implementing API security standards in their production environment. Join industry experts from EMA Associates and 42Crunch as they explore why business cannot let API Security to be an afterthought.
Build Secure APIs in VS Code with Instant API Security Testing
Webinar showcasing how 42Crunch’s API Audit and API Scan tools integrate within VS Code allowing developers to instantly audit and test their APIs as they code.
Protect Your APIs with Microsoft Azure Sentinel and 42Crunch Platforms
This webinar showcases how users of the Microsoft Azure Sentinel platform via the 42Crunch platform integration can proactively protect their APIs. By leveraging 42Crunch’s API security platform, Azure Sentinel users gain visibility into their API infrastructure, identify vulnerabilities, and mitigate risks.
Review of the Major API Breaches from H2 2022
Colin Domoney reviews some of the major API breaches that occurred in the second half of 2022. In the webinar, he outlines the API vulnerabilities that were compromised during the attacks and shows how to protect against them.
Defending APIs with Jim Manico
Technical talk from 42crunch and Manicode on request forgery (CSRF and SSRF) to help software developers build secure web applications and APIs.
Hacking APIs for Fun & Profit
Join Colin Domoney, Developer Advocate at 42Crunch in discussion with Adrian and Bogdan Tiron, Managing Partners at FORTBRIDGE as they discuss their careers as pen testers, and in particular their recent experiences in testing and exploiting API-based products.
Review of the Major API Breaches from H1 2022 – Episode 2
This is a two-part webinar series on the global API breaches from H1 2022 that made the news. The first session described the breaches at a high level (recording below) and the second describes how to defend against them.

Benefits of a Positive Security Model for APIs
Positive Security is a model that enables access to known trusted resources rather than trying to determine what activity or entities have hostile intent. Applying a positive security model when protecting your APIs can offer direct benefits such as reduction in false negatives, lower reliance on constantly adding characteristics of hostile traffic, and others. It also has indirect benefits for the working groups on your DevSecOps team that allow them to focus and be more efficient in their individual roles.

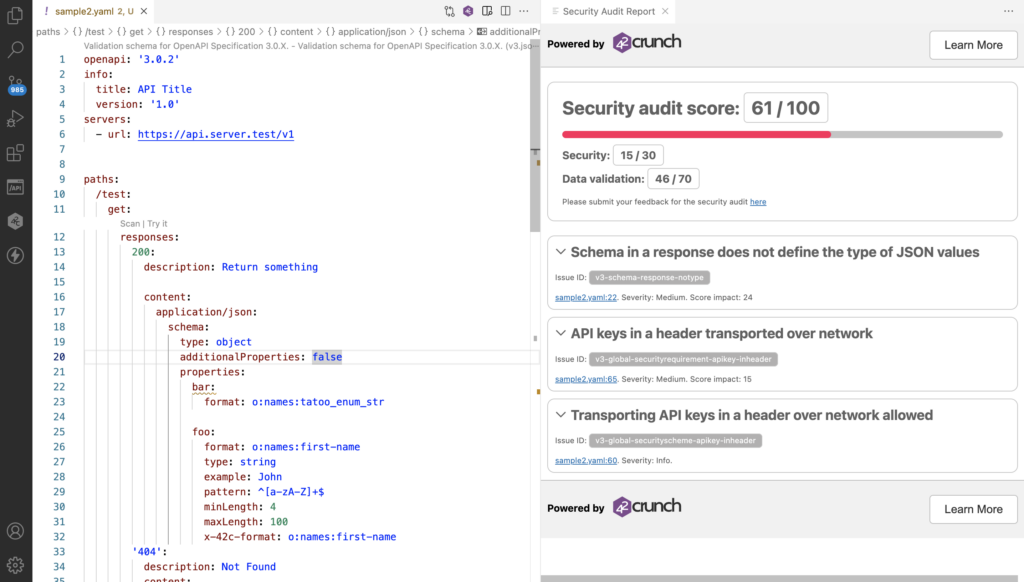
REST API Risk Audit – Online Demo
In this session, 42Crunch technical expert, Andy Wright, walks through how to perform a Security Audit and a Conformance Scan of your API Contract. He immediately builds a security report and calculates an audit score for each API he analyzes based on the OpenAPI annotations in the API definition. This audit score reflects the risk associated with exposing the APIs, internally and externally.
Review of the Major API Breaches from H1 2022 – Episode 1
This is a two-part webinar series on the global API breaches from H1 2022 that made the news. The second part of this webinar series explores how to defend against common API security breaches covered in the first part of the series. Join Colin Domoney (42Crunch security researcher and curator of the APISecurity.io newsletter) to understand how to use defensive techniques to protect APIs. This practical and interactive webinar will illuminate how APIs can be protected against common attack types and real-world exploits.

Actively Monitor and Defend Your APIs with 42Crunch and the Azure Sentinel Platform
In this webinar 42Crunch and CyberProof demonstrate how to proactively integrate API access logs into the Microsoft Azure Sentinel platform and actively defend APIs with the 42runch API Micro-Firewall

OWASP API Security TOP 10 Challenges – Episode 3
In this 3-part webinar series Dr. Philippe De Ryck, Web Security Expert with Pragmatic Web Security and Colin Domoney of 42Crunch and APISecurity.io, take a deep dive into understanding and addressing the OWASP API Security Top 10 issues. Through detailed practical examples and use cases, they guide developers and security professionals through how to fix and secure their APIs in the face of these identified threats.

OWASP API Security Top 10: Comprendre les menaces qui ciblent les APIs
Ce webinaire, dédié à la sécurité des APIs, traite des menaces listées par l’OWASP API Security top 10. Vous assisterez à l’explication détaillée de chaque menace, son exploitation possible, des exemples d’attaques réussies et comment, grâce à la technologie 42crunch il est possible de s’en prémunir.

How to Extend Protection of your Data from API to Mobile Application
This webinar presents the new integration of 42Crunch with comprehensive mobile app protection from Approov. A joint solution that delivers shift-left API protection as well as run-time shielding that extends all the way to your mobile apps and the environments they run in.

OWASP API Security TOP 10 Challenges – Episode 2
THREE-PART WEBINAR SERIES May 4th, 2022 | 8am PST | 4pm BST Watch the Webinar Browse the Deck In this first episode in the webinar series, Dr Philippe de Ryck and Colin Domoney discuss API security today and the challenges presented by the OWASP API security top 10. Questions from attendees were addressed throughout the […]

OWASP API Security TOP 10 Challenges – Episode 1
In this first episode in the webinar series, Dr Philippe de Ryck and Colin Domoney discuss API security today and the challenges presented by the OWASP API security top 10. Questions from attendees were addressed throughout the webinar.

Automate your API security with Security as Code
Traditionally developers like to focus on the data and functionality of their APIs while the security team is concerned with the enforcement of API security controls and policies. This siloed approach has led to inefficiencies and bottlenecks in the DevSecOps’ cycle that are delaying the release of APIs and creating cost over runs.

Protección efectiva de sus APIs y Microservicios
Tus APIs están en riesgo, punto! Muchas organizaciones tienen la epifanía de que tener los componentes tradicionales como WAF y las capacidades tradicionales de los API Gateways son suficientes para que estén protegidas, pero no lo están.

Diseñando API seguras usando la plataforma 42Crunch con Postman
Diseñando APIs seguras usando la plataforma 42Crunch con Postman

Why Continuous API Security is key to protecting your Digital Business
Join these experts as they discuss the benefits of an integrated, continuous, and proactive approach to API security that combines proactive application security measures with continuous activity monitoring, API-specific threat analysis, and runtime policy enforcement.

Integrating 42Crunch API Contract Security Testing within Postman
Kin Lane, chief Evangelist with Postman recently joined Isabelle Mauny, Field CTO at 42Crunch for a webinar to demonstrate how enterprises are automating the testing of API security for all their APIs.

Dissecting the Biggest API Breaches from Q1 2021
API Security can be hard and confusing, but learning from someone else’s mistakes is the best way to learn!

API Security for Global Enterprises – Successful and unsuccessful approaches to API Security
Join 42Crunch and special guest speaker Darren Shelcusky, Manager of Vehicle & Connectivity Cybersecurity at Ford Motor Company, as he takes us through their approach to API security and journey to enforce security compliance while ensuring productivity of their hundreds of developers managing thousands of APIs.

API Security in a Kubernetes World
Securing APIs deployed in Kubernetes implies securing the infrastructure, but also the APIs themselves. Having a perfectly setup cluster, with all possible protections in place, is only ONE aspect of the measures you need to take to prevent the vulnerabilities listed in the OWASP API Security Top 10. Other issues such as data leakage, mass assignment or broken authentication must be handled at the application level.

How to Best Leverage JWTs for API Security
JSON Web tokens (JWTs) are used massively in API-based applications as access tokens or to transport information across services. Unfortunately, JWT standards are quite complex and it’s very easy to get the implementation wrong. As a result, data breaches and API vulnerabilities due to poor JWT implementation, token leakage, and lack of proper validation remain widespread.

OWASP API Security Top 10 Webinar Series (Part 2)
By now, you should know that APIs are special and deserve their own OWASP Top 10 list, but do you know how these common attacks happen and why?

OWASP API Security Top 10 Webinar Series (Part 1)
By now, you should know that APIs are special and deserve their own OWASP Top 10 list, but do you know how these common attacks happen and why?

OAuth, OWASP, Gateways and Meshes – Oh my!
To consider and apply API security effectively, we need to understand where we are and where we need to go. We need to know the tools we have available and who our allies are. Finally, we need a clear path and priorities on what we can accomplish and how. In this webinar, we’ll lay out a reference architecture to ensure we understand the scope, challenges, and approach to secure your APIs and organization as a whole.

OpenAPI for API Security (Why Guess when you know?)
According to the State of the APIs report released by Smartbear in 2019, 80% of developers use OpenAPI to describe their APIs (you may still call it Swagger, but you really should call it OpenAPI now!)

Let’s shift API Security Left! Sure, but how?
API security flaws are injected at many different levels of the API lifecycle: in requirements, development and deployment. It is proven that detecting and fixing vulnerabilities during production or post-release time is up to 30 times more difficult than earlier in the API lifecycle.

42Crunch Security Audit for WSO2 API Manager 3.1
WSO2 API Manager 3.1 brings a lot of interesting features including the ability to run 42Crunch’s audit tool directly from the API Publishing portal.

Top API Security Issues Found During POCs
Over the past 6 months, we have discovered many similarities across APIs from companies from very different industries. “This is an eye opener” is the most recurring comment from our prospects. We thought it would be worth sharing our findings in this webinar.

The Anatomy of API Breaches
Securing APIs implies securing the infrastructure but also the APIs themselves. Unfortunately, having all possible infrastructure protections in place is only one aspect of the recent OWASP Top10 for API Security. Other issues such as data leakage, mass assignment or broken authentication/authorization must be handled at the application level.

REST API Security for Microsoft Azure Pipelines
Security is an important topic in software development. Unfortunately, security is usually considered too late in software development, and especially in the API lifecycle. Waiting until software and APIs are in production before addressing security concerns can be a severe risk to your organization. Did you know that vulnerabilities found in production cost up to 30x time and money more to fix?

Protecting Microservices APIs with 42Crunch API Firewall
In loosely coupled architectures, we must put in place application level security, should it be for client traffic (North-South) or intra-microservices traffic (East-West).

Are You Properly Using JWTs?
JSON Web tokens (JWTs) are used massively in API-based applications as access tokens or to transport information across services. Unfortunately, JWT are often mis-used and incorrectly handled. Massive data breaches have occurred in the last 18 months due to token leakage and lack of proper of validation.

Positive API Security Model, and Why You Need It!
Many of the issues on the OWASP API Security Top 10 are triggered by the lack of input or output validation.

OWASP API Security Top 10
In recent years, large reputable companies such as Facebook, Google and Equifax have suffered major data breaches that combined exposed the personal information of hundreds of millions of people worldwide. The common vector linking these breaches – APIs. The scale and magnitude of these breaches are the reason API security has been launched into the forefront of enterprise security concerns – now forcing us to rethink the way we approach API security as a whole.
Secure Your APIs Today
#1 API security platform

