Tutorials
API Security Testing with API Scan
We are going to show you how to perform a conformance scan on our platform. You can also perform an API Scan in VS code IDE (platform registration is required). You can register for free. API Scan is a dynamic runtime testing tool that simulates real traffic to your API to ensure conformance with the OpenAPI contract and identify security vulnerabilities.
Dynamic Testing
API Contract Conformance Scan is a dynamic runtime analysis of your API to check that the behavior of the API conforms to the contract it advertises in its OpenAPI (formerly known as Swagger) definition.
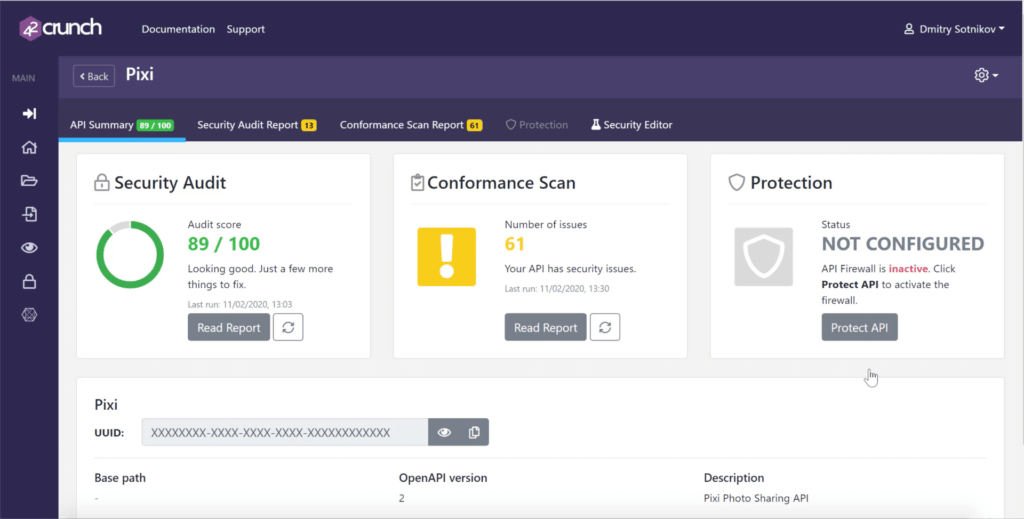
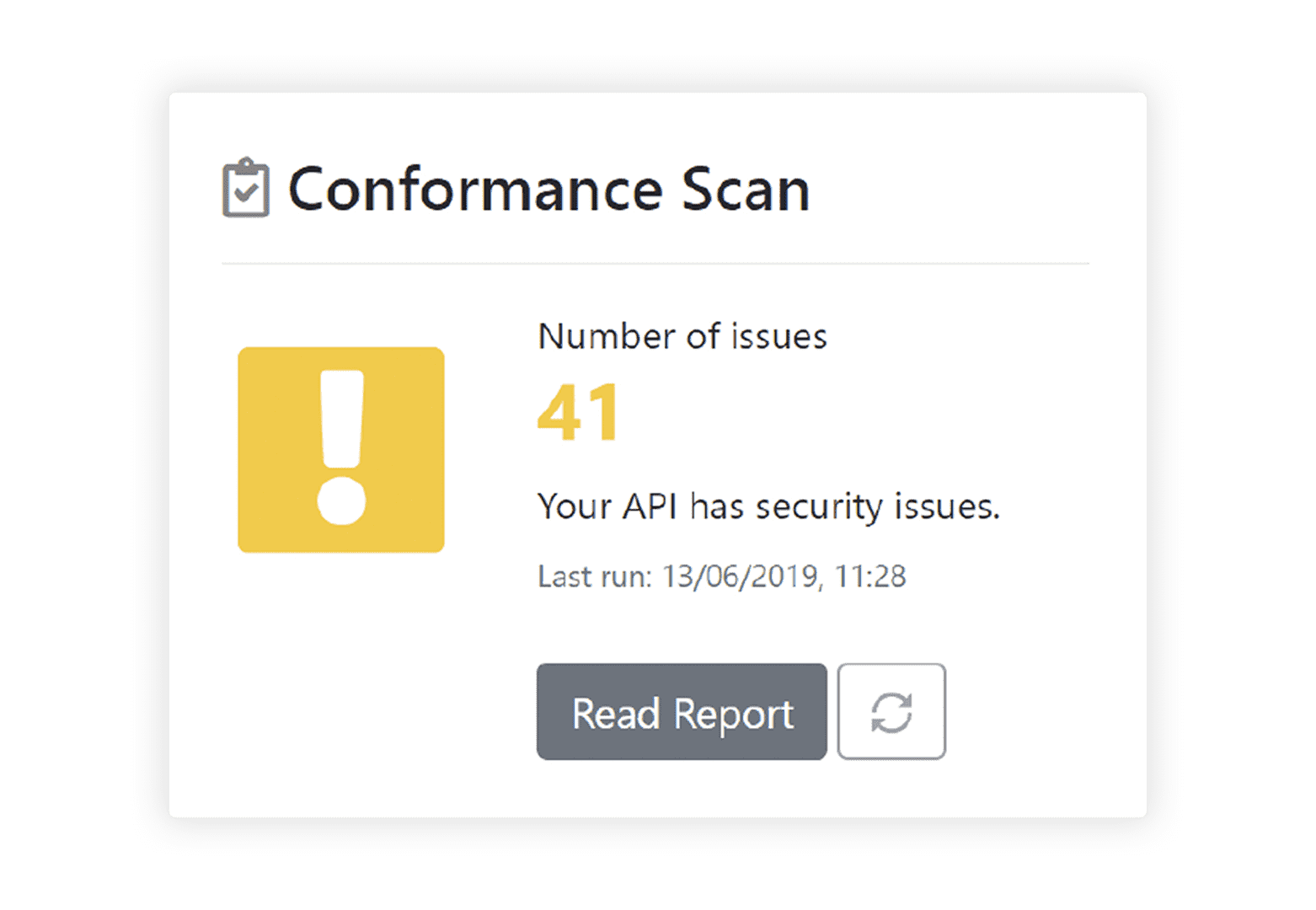
You can run a scan on an API you have imported to 42Crunch Platform and deployed to find out if there are any mismatches between the API definition describing your API and what it actually does. If Conformance Scan testing finds any discrepancies, it reports the issues clearly so that you can fix them.
Authentication in Conformance Scan
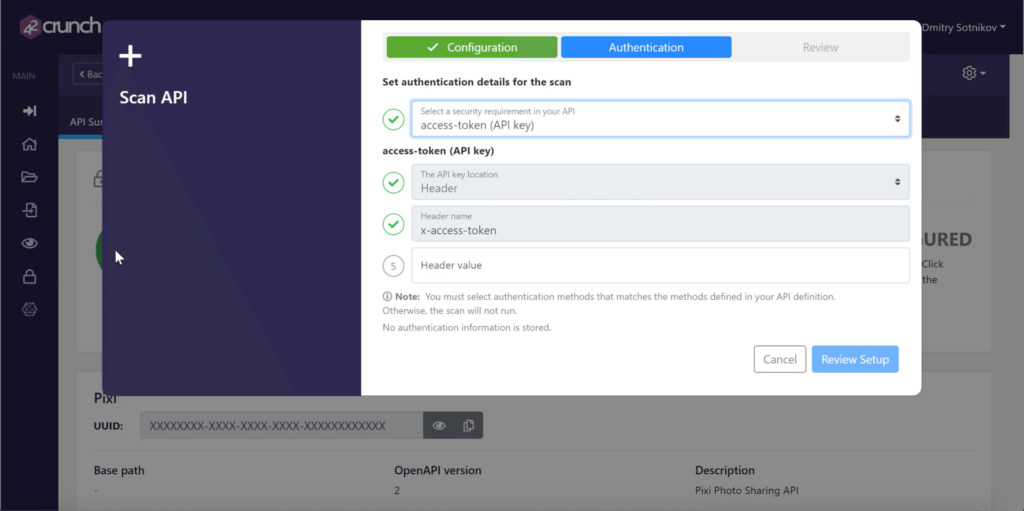
If you have defined security requirements in your API, Conformance Scan must provide the information to fulfill those requirements when it sends requests to the API. When you configure the scan, you must therefore fill in the details that Conformance Scan can use to authenticate.
The configuration wizard shows the security requirements defined on the root level in the OpenAPI (Swagger) definition of your API in a drop-down list. Each line on the list corresponds to a security requirement in the API definition, and the text lists the names of the security schemes and their types in that security requirement.
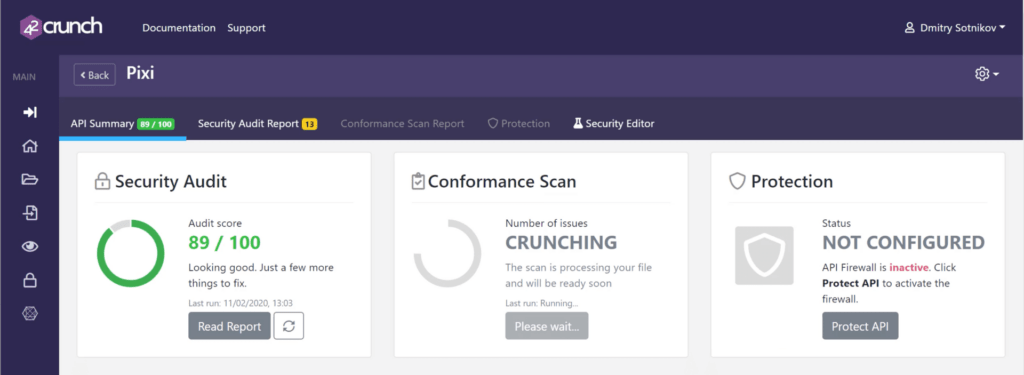
Now 42Crunch fuzzes the OpenAPI (Swagger) file by sending it requests outside of the contract: different paths, different verbs, different transports, different parameters. Each and every one of these requests are not compliant with the contract, and SHOULD get rejected.
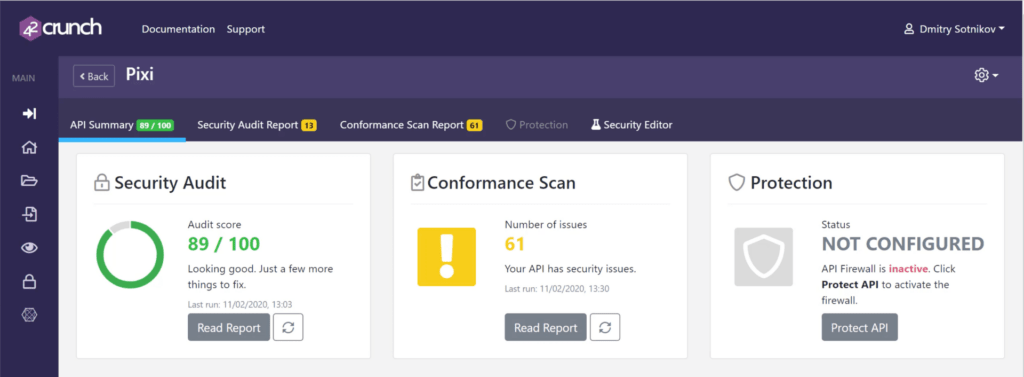
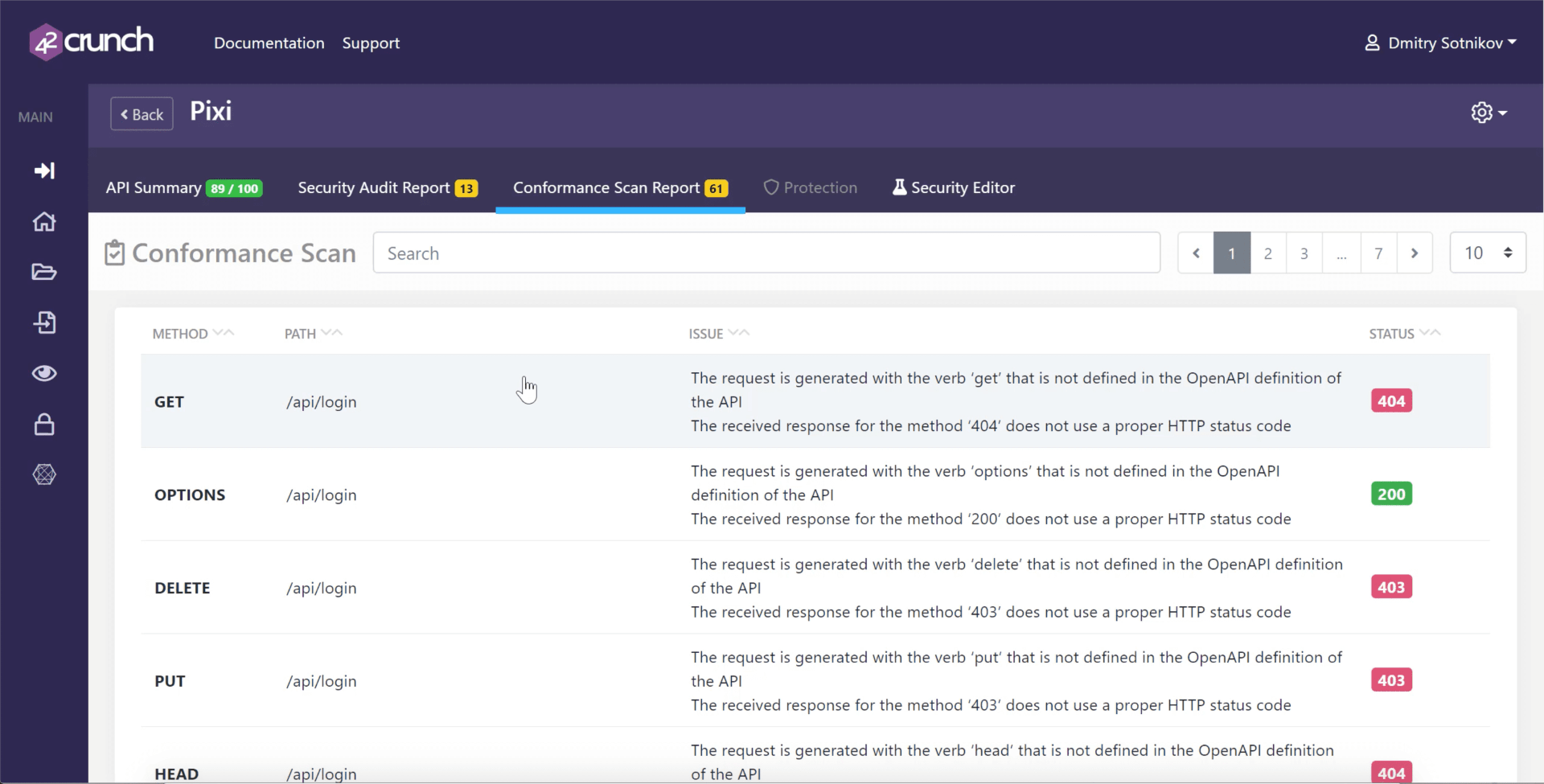
In this particular case 61 requests that were invalid did not get rejected. All of these discrepancies are potential vulnerabilities that we were not aware of. So, the backend code somehow still works with these inputs that are not valid. Typically APIs are tested for scenarios within the design of the API – by fuzzing outside of the contract, we are able to find unknown vulnerabilities that could have led to a data breach.
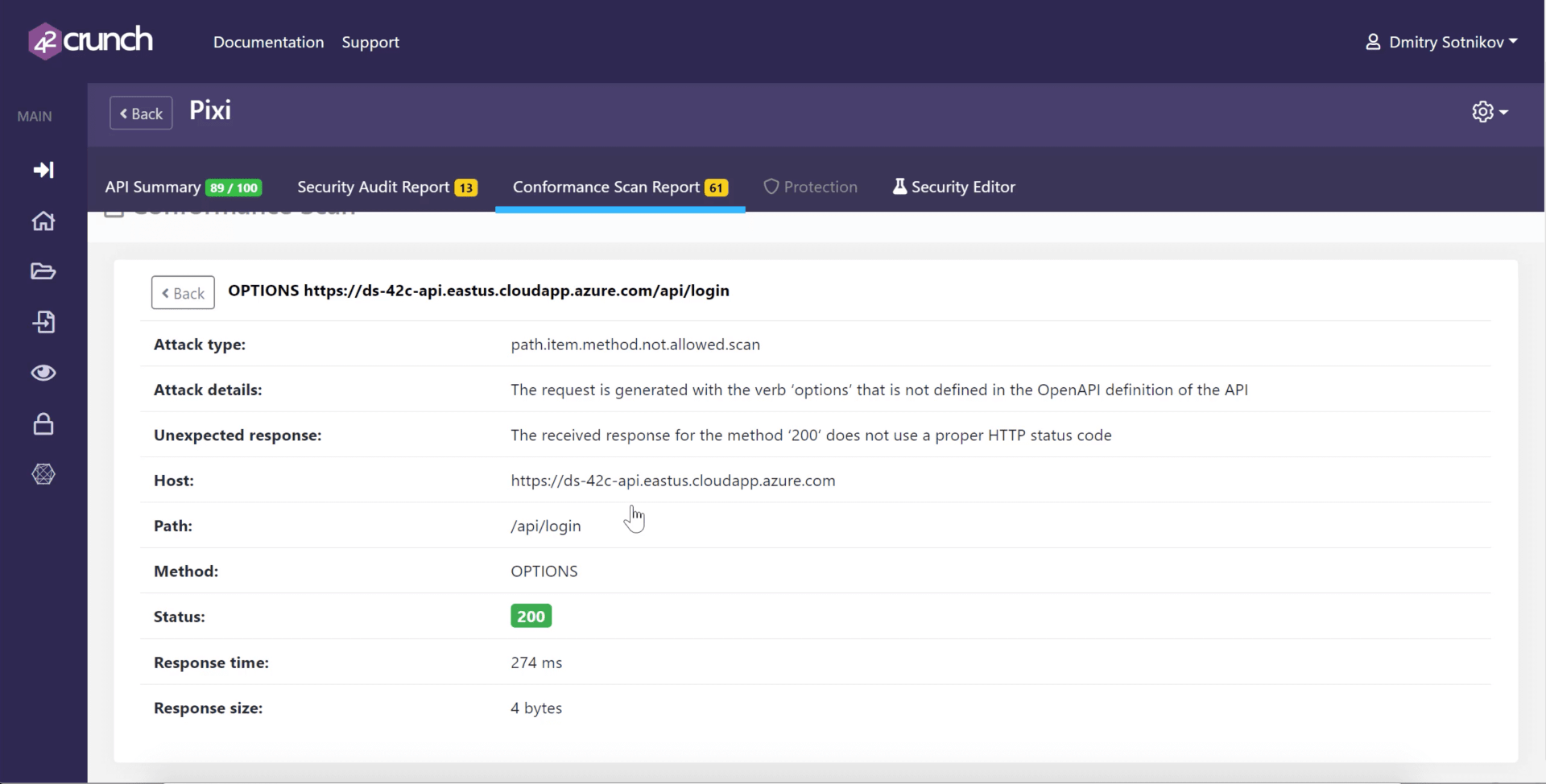
Scan Report
Conformance Scan produces a scan report that provides valuable information on how well your API conforms to its API definition. The report summarizes what was scanned and how the scan went, including the API’s response times, the received HTTP status codes, as well as any unexpected response status codes and their reasons. Clicking a found issue provides further details on it.
Try API Scan for Free
- Dynamic runtime testing that simulates real traffic to your API.
- Tests conformance to the audited OpenAPI Contract.
- The instant report provides automated and guided fixes in-line with code.




